Recommendations
- Create a quarterly review process for business-critical automations. If no one can explain what an automation does, who owns it, and how it would be recovered after a failure, treat it as an operational risk requiring remediation.
- Build an automation inventory that captures owners, dependencies, credentials, recovery procedures, and business impact. You cannot manage risks associated with automations you cannot identify.
- Require every production automation to have a one-page operational runbook that explains purpose, inputs, outputs, dependencies, common failure scenarios, and recovery steps.
- Prioritize the top 10 automations that would have the greatest business impact if they failed tomorrow. Focus documentation, testing, and ownership efforts there before attempting broader coverage.
- Include maintainability metrics in automation success criteria. Delivery is not complete until ownership, documentation, monitoring, and support processes are established.
Automation is often sold as the cure for operational dependency. Build the workflow once, remove manual effort, and let the system run consistently at scale. In theory, automation reduces risk because work no longer depends on tribal knowledge or individual heroics.
Yet in many organizations, the opposite has happened.
Critical automations now run payroll feeds, onboarding tasks, invoice routing, access provisioning, customer notifications, data transfers, reconciliations, and infrastructure jobs—but nobody fully understands how they work anymore. The original builder left years ago. Documentation was never finished. Exceptions were added in production. Integrations changed over time. The automation still runs, so everyone leaves it alone.
And that creates a dangerous kind of stability: fear-based inertia.
The process appears reliable because no one touches it. But the moment the business needs to scale, migrate, audit, troubleshoot, or change policy, the real cost becomes clear.
The Rise of the “Black Box” Automation
Most fragile automations did not begin as failures. They began as wins.
A repetitive task was automated quickly. A script saved hours each week. A workflow reduced backlog. A bot eliminated manual rekeying. The business saw immediate value, and momentum grew.

Then the system evolved.
A new approval rule was added. An exception path was hardcoded. Credentials changed. A downstream application was replaced. Someone patched the logic during an incident. Another team copied the workflow for a different use case. Over time, what started as a clean solution became a layered artifact of every operational change around it.
This pattern is common in enterprise technology. Systems accumulate complexity incrementally, especially when speed is rewarded more than maintainability. Research in software engineering has long described this as technical debt: short-term decisions that create long-term cost and fragility.
Why Nobody Wants to Touch It
When teams avoid modifying automation, it is rarely because they do not care. It is because the perceived risk is high and the understanding is low.
No one knows what will break if one condition changes. Dependencies are unclear. There is no safe test environment. Logs are incomplete. Business owners only notice the automation when it fails. The person closest to it inherited responsibility rather than designing it.
So the organization develops a silent rule: do not touch the thing that still works.
That instinct is understandable. It is also expensive.
Fear-based inertia delays policy updates, slows improvement initiatives, blocks modernization, and turns minor fixes into executive escalations. Teams spend more energy avoiding change than enabling it.
Studies on organizational routines have shown that when knowledge is embedded in systems rather than shared across people and documentation, organizations become less adaptable even if day-to-day execution appears stable.
The Hidden Operational Risk
Undocumented automation creates risks that are easy to underestimate because they remain invisible until triggered.

A credential expires and no one knows where it is stored. A regulatory requirement changes but the workflow still applies old logic. A cloud migration breaks a dependency buried in a script. A key employee leaves and no one can support month-end processing. An audit asks how approvals are enforced, but there is no clear evidence beyond “the system does it.”
These are not hypothetical scenarios. They happen because operational resilience depends on understanding, not just execution.
Research on operational resilience shows that organizations reduce disruption risk when they understand dependencies across people, processes, technology, and third parties rather than treating resilience as only a disaster recovery issue.
The irony is sharp: automation meant to reduce dependency can become the dependency.
Documentation Is Not Bureaucracy
Many teams treat documentation as optional overhead—something to do later when there is time. Later rarely comes.
But documentation is not paperwork for its own sake. It is an operational control.
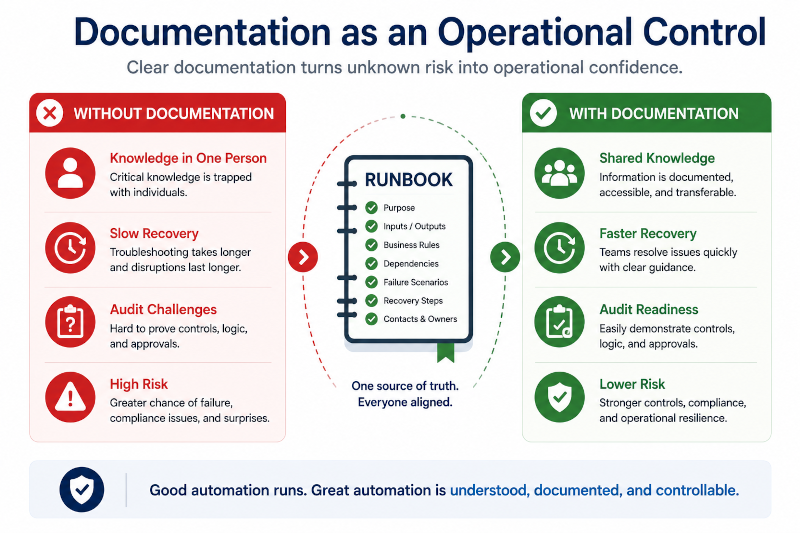
Useful documentation explains purpose, inputs, outputs, business rules, dependencies, credentials, owners, failure modes, and recovery steps. It tells the next person how the automation works and how to change it safely. It reduces onboarding time, lowers incident response stress, and makes audits faster.
Research on knowledge management consistently finds that organizations perform better when tacit knowledge is converted into accessible, reusable knowledge rather than remaining trapped in individuals or opaque systems.
Without that conversion, every handoff increases risk.
What Healthy Automation Looks Like
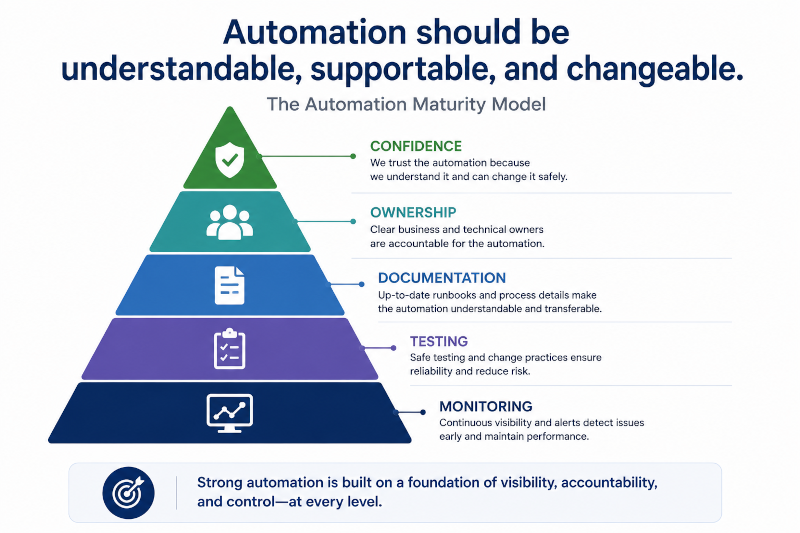
The goal is not to document every line of code in isolation. The goal is to make critical automations understandable, supportable, and changeable.
Start by identifying business-critical workflows. Which automations would materially disrupt operations if they failed tomorrow? Prioritize those first.
Assign clear ownership. Every automation should have both a technical owner and a business owner. If everyone uses it but no one owns it, it is already a risk.
Map dependencies. Know what systems, credentials, APIs, schedules, and approvals the automation relies on.
Create readable runbooks. Focus on practical knowledge: what it does, where it runs, how to monitor it, common failure points, and how to recover.
Build safe change paths. Use version control, testing environments, peer review, and rollback plans. Teams are less afraid to improve systems when change feels controlled.
Review periodically. Business rules change. Applications change. Compliance obligations change. Automation that never gets reviewed eventually becomes misaligned.
The Culture Problem Behind the Technical Problem
Many organizations know they have undocumented automations. They delay action because the systems still appear functional.
That is not a tooling issue. It is a governance issue.
When incentives reward delivery speed only, maintainability gets deprioritized. When no time is allocated for cleanup, complexity compounds. When leaders celebrate launches but ignore ownership gaps, fragile systems multiply quietly.
Healthy automation requires treating maintainability as part of delivery, not separate from it.
Final Thought
If nobody knows how an automation works, it is not truly automated—it is merely unattended.
And if everyone is afraid to touch it, the business is not stable. It is one change request away from disruption.
The strongest automation programs are not built on mystery. They are built on transparency, ownership, and confidence that systems can evolve safely. Because in a changing business, the real value of automation is not that it runs today. It is that it can adapt tomorrow.


1 thought on “Nobody Knows How This Automation Works”