Recommendations
- Map all third-party systems, vendors, integrations, and external access pathways as part of the organization’s active attack surface rather than treating them as separate external entities.
- Treat vendor-connected systems as extensions of the internal enterprise environment and apply equivalent monitoring, segmentation, and governance controls wherever possible.
- Continuously review and reduce third-party access privileges, dormant accounts, and inherited permissions across vendor-connected systems.
- Shift vendor risk programs from static compliance reviews toward continuous operational monitoring, access visibility, and resilience assessment models.
- Integrate vendor risk management directly into enterprise resilience planning, operational continuity exercises, and executive governance discussions rather than isolating it inside procurement or compliance teams alone.
Most organizations have spent years strengthening internal cybersecurity defenses. They deploy endpoint detection systems, identity management platforms, multi-factor authentication, zero trust architectures, cloud monitoring tools, and AI-assisted threat detection environments. In many enterprises, internal cybersecurity maturity has improved substantially over the last decade.
And yet, attackers are increasingly bypassing those defenses altogether. They are entering through vendors, suppliers, contractors, managed service providers, APIs, SaaS platforms, and software dependencies already trusted inside the organization.
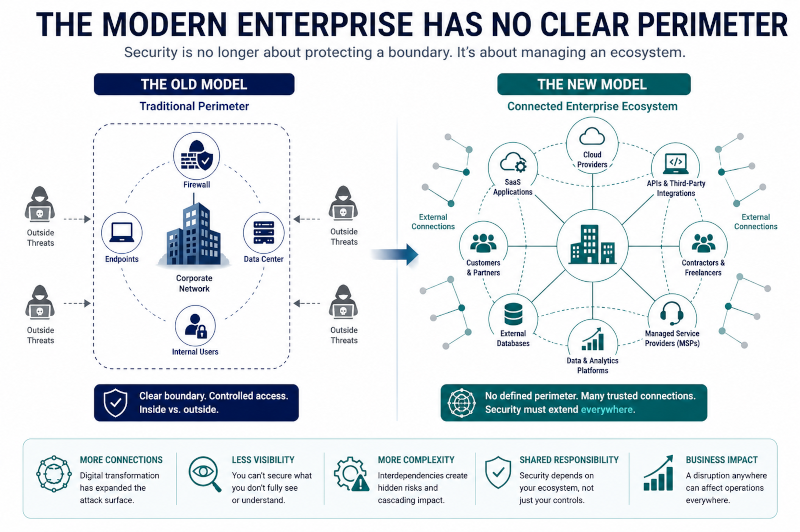
This shift reflects a much larger transformation in how modern enterprises operate. Organizations are no longer isolated environments with clearly defined perimeters. They function as interconnected operational ecosystems dependent on third-party platforms, cloud infrastructure, software integrations, outsourced services, and external business partners.
Every one of those dependencies expands the attack surface.

Gartner projected that 45% of organizations worldwide would experience attacks on their software supply chains by 2025, representing a major increase compared to previous years. The World Economic Forum has similarly identified cyber supply chain insecurity and ecosystem complexity as growing systemic business risks affecting organizations globally.
The implications extend far beyond traditional cybersecurity.
Third-party compromise now affects:
- operational continuity,
- regulatory exposure,
- customer trust,
- AI systems,
- cloud environments,
- and enterprise resilience simultaneously.
As explored previously in Small Businesses Underestimate Insider Risk, modern security problems often emerge through operational trust structures rather than dramatic external attacks alone. Vendor ecosystems amplify this challenge because organizations routinely extend trusted access to external entities embedded deeply inside daily operations.
The future of cybersecurity may therefore depend less on protecting isolated infrastructure and more on understanding the operational ecosystems organizations depend on continuously.
Recommendation: Map all third-party systems, vendors, integrations, and external access pathways as part of the organization’s active attack surface rather than treating them as separate external entities.
The Modern Enterprise Perimeter No Longer Exists
For decades, cybersecurity strategies focused heavily on defending organizational boundaries. Enterprises secured internal networks, hardened endpoints, monitored inbound traffic, and attempted to prevent unauthorized external access.
That model no longer reflects how modern enterprises function.
Cloud platforms, SaaS applications, remote work environments, APIs, contractors, and external service providers now operate as embedded components of day-to-day business activity. Many organizations rely on dozens or even hundreds of third-party services simultaneously to support finance, HR, logistics, software development, communications, customer support, and operational coordination.
This creates a difficult reality: many organizations no longer fully control the environments their operations depend on.
Research from the National Institute of Standards and Technology (NIST) highlights that third-party relationships substantially expand organizational attack surfaces while introducing visibility and governance limitations beyond what many internal security teams can effectively monitor.
Attackers understand this well.
Instead of targeting hardened enterprise environments directly, threat actors increasingly compromise trusted suppliers, software providers, remote support environments, or cloud-connected systems capable of providing downstream access into larger organizations.
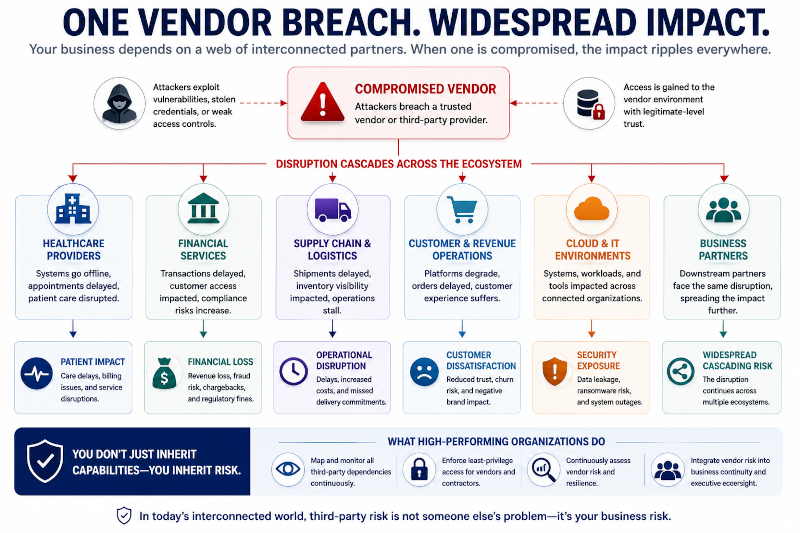
The 2024 Change Healthcare cyberattack demonstrated how operationally devastating these dependencies can become. After attackers compromised the healthcare technology provider, hospitals, pharmacies, insurers, and healthcare networks across the United States experienced widespread operational disruption affecting prescriptions, billing, claims processing, and patient services. The breach did not remain isolated inside a single organization. It cascaded through an interconnected ecosystem dependent on shared infrastructure.
The SolarWinds attack remains another defining example. Attackers inserted malicious code into software updates distributed through trusted IT management systems, ultimately impacting thousands of organizations including government agencies and major enterprises. The compromise succeeded not because organizations lacked internal defenses, but because attackers exploited trusted operational relationships already embedded inside enterprise environments.
This represents one of the most important shifts in modern cybersecurity: organizations are no longer defending only their own infrastructure. They are defending ecosystems of inherited dependencies.
That distinction changes cybersecurity fundamentally.
Recommendation: Treat vendor-connected systems as extensions of the internal enterprise environment and apply equivalent monitoring, segmentation, and governance controls wherever possible.
Why Vendors Have Become the Ideal Attack Path
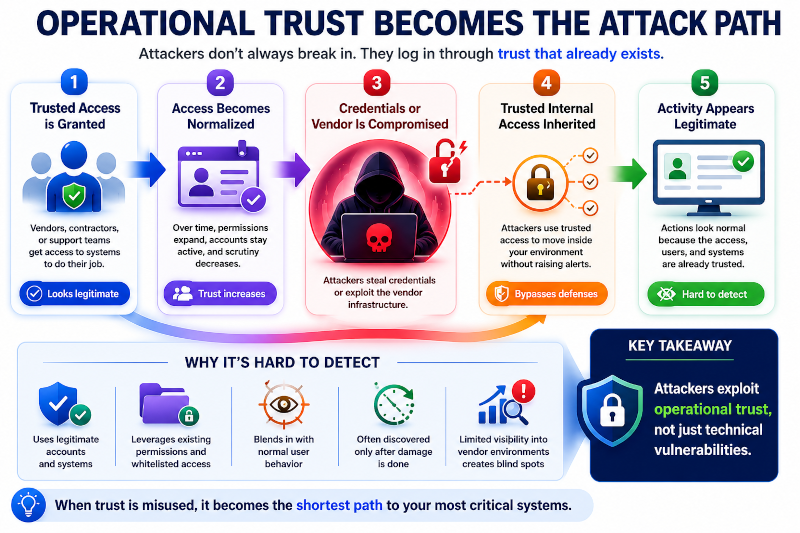
From an attacker’s perspective, vendors offer several strategic advantages.
Compromising a single software provider, cloud platform, contractor account, or managed service environment can provide access into hundreds or thousands of downstream organizations simultaneously. Vendor activity is also frequently trusted operationally, which means security teams often apply less scrutiny to external systems already integrated into internal workflows.
This creates a dangerous combination of:
- scale,
- trust,
- and reduced visibility.
A common example appears in large enterprise support environments. Contractors or third-party support teams may receive access to collaboration platforms, ticketing systems, administrative dashboards, remote management tools, or cloud infrastructure in order to support operational continuity. Over time, that access often becomes normalized. Permissions expand gradually, accounts remain active longer than necessary, and monitoring becomes less aggressive because the activity appears operationally legitimate.
If the vendor environment becomes compromised — or if attacker-controlled credentials are inherited through phishing, malware, or weak governance — threat actors may gain trusted internal access without triggering the same scrutiny associated with external intrusion attempts.
In many cases, attackers are not exploiting highly sophisticated vulnerabilities.
They are exploiting operational trust.
This is what makes third-party risk especially difficult to detect. The activity frequently appears normal until significant damage is already underway.
The Okta third-party support breach illustrated this challenge clearly. Attackers accessed customer support systems through compromised credentials associated with an external support provider, exposing customer session tokens and creating downstream security exposure for connected organizations. The incident reinforced how operational trust relationships inside support ecosystems can become critical attack vectors even when the core platform itself maintains strong security controls.
Research from IBM’s 2025 Cost of a Data Breach Report found that breaches involving third-party compromise and supply chain relationships often generate particularly high financial and operational costs because organizations inherit both direct security exposure and cascading business disruption simultaneously.
This creates a larger operational reality many organizations still underestimate:
security exposure is increasingly inherited through business dependencies rather than created solely inside internal systems.
Recommendation: Continuously review and reduce third-party access privileges, dormant accounts, and inherited permissions across vendor-connected systems.
Compliance Does Not Equal Security
One of the most persistent misconceptions surrounding vendor risk is the assumption that compliance frameworks automatically indicate strong security maturity.
Organizations often rely heavily on:
- SOC 2 reports,
- ISO 27001 certifications,
- security questionnaires,
- procurement reviews,
- or onboarding assessments
to evaluate vendors.
Those controls matter, but they have important limitations.
Most compliance reviews function as point-in-time evaluations rather than continuous operational assessments. A vendor may pass security audits successfully while still maintaining:
- weak access governance,
- fragmented monitoring,
- inconsistent patching practices,
- or insufficient operational resilience.
This creates what many organizations mistakenly interpret as security certainty.
The problem becomes even more complicated because vendor reviews are frequently checklist-driven rather than operationally integrated. Security teams distribute questionnaires during procurement, review documentation during onboarding, and then revisit the vendor only periodically afterward despite evolving threat conditions, architectural changes, or expanding integrations.
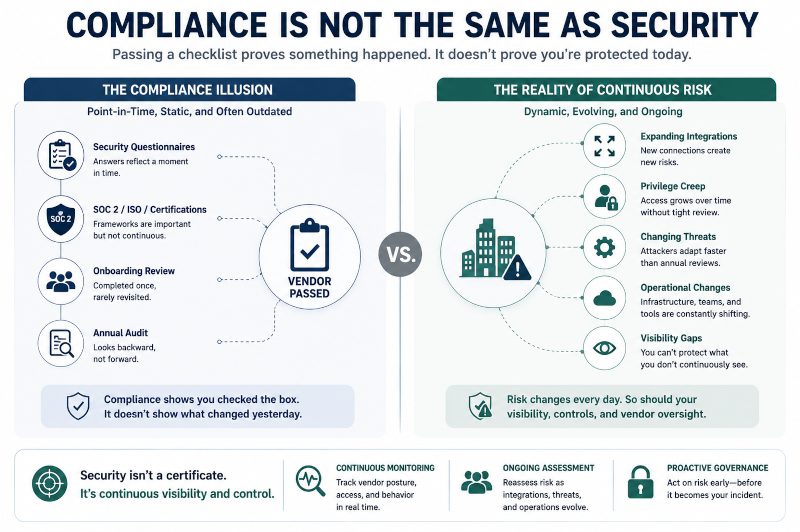
The World Economic Forum’s cybersecurity research notes that supply chain opacity and limited visibility remain major systemic weaknesses across modern digital ecosystems.
In practice, many organizations understand surprisingly little about:
- how vendors manage privileged access,
- how quickly incidents are detected,
- how dependencies are segmented,
- or how operational resilience functions during disruption events.
This creates a dangerous illusion:
vendors may appear compliant while remaining operationally fragile.
As explored previously in Most Organizations Don’t Have Processes — They Have Habits, many enterprises still rely heavily on informal operational behaviors hidden beneath formal governance structures. Third-party ecosystems often magnify those inconsistencies because organizations inherit operational practices they do not directly control.
The larger issue is not merely technical.
It is organizational.
Modern enterprises often outsource operational capability faster than they mature governance visibility.
Recommendation: Shift vendor risk programs from static compliance reviews toward continuous operational monitoring, access visibility, and resilience assessment models.
Vendor Risk Is Becoming a Business Continuity Problem
One of the most important changes underway is that supply chain cybersecurity is no longer viewed solely as a technical issue.
Vendor-related incidents now create direct business disruption.
A compromised provider can interrupt:
- logistics,
- healthcare delivery,
- customer support,
- payment systems,
- manufacturing operations,
- AI environments,
- or cloud infrastructure coordination
across entire business ecosystems.
This is one reason vendor risk discussions are moving closer to executive leadership and board-level governance conversations. Organizations increasingly recognize that modern operational continuity depends heavily on external systems they do not fully control.
McKinsey research examining operational resilience found that interconnected dependencies create growing systemic exposure because disruption inside one provider can propagate rapidly across downstream organizations and workflows.
AI adoption may amplify this challenge further.
As organizations integrate AI systems into workflows, many become dependent on external AI providers, cloud environments, APIs, retrieval systems, and model ecosystems supporting operational execution. This creates additional inherited exposure because organizations may not fully understand:
- how models are secured,
- how data flows between systems,
- or how disruptions inside AI infrastructure providers affect downstream operations.
As explored previously in AI Is Becoming an Operational Layer, Not Just a Productivity Tool, intelligent systems are becoming embedded directly into enterprise coordination environments rather than functioning as isolated tools. That deeper integration means third-party disruption now affects not only infrastructure, but operational execution itself.
The strongest organizations are beginning to adapt accordingly.
Rather than treating vendors as external entities outside the operational environment, mature organizations increasingly view vendors as interconnected components of enterprise risk architecture.
That mindset shift may become one of the defining cybersecurity transitions of the next decade.
The future of cybersecurity may depend less on defending isolated networks and more on managing trust across interconnected ecosystems operating under constant dependency complexity.
Organizations no longer inherit risk only from the systems they build internally.
Increasingly, they inherit risk from the ecosystems they depend on daily.
Recommendation: Integrate vendor risk management directly into enterprise resilience planning, operational continuity exercises, and executive governance discussions rather than isolating it inside procurement or compliance teams alone.

